Leaderboard
Popular Content
Showing content with the highest reputation on 11/11/2024 in all areas
-
3 points
Time Left: 6 years and 23 days
- FOR SALE
- NEW
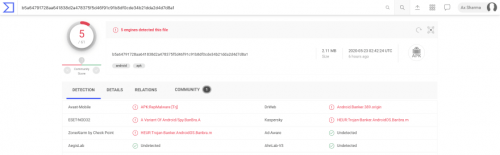
☢️ Dissecting DEFENSOR: a stealthy Android banking malware #android#apps#malware#mobile Android malware apps are nothing new, but this one is of particular interest in how it implements no such functionality that can be readily detected by security products. The apps named DEFENSOR ID and Defensor Digital rely mainly on Android's Accessibility Service to conduct malicious activities, and go undetected. In fact, a blog post released May 22nd 2020 by malware researcher Lukas Stefanko of ESET states, "the banking trojan was available on Google Play at the time of the analysis. The app is fitted with standard information-stealing capabilities; however, this banker is exceptionally insidious in that after installation it requires a single action from the victim – enable Android’s Accessibility Service – to fully unleash the app’s malicious functionality." The blog post also demonstrates at the time of its inception, no antivirus engine detected this malware sample. Even today, only 5-6 detection engines are flagging these two apps, according to VirusTotal. This raises concern for the next iteration of malware that may be nothing but a slight modification of these apps. Android Accessibility Service To make smartphones more accessible to users with special needs, the Accessibility Service allows for the device to extend permissions to an app to read screen content (e.g. for providing text to speech synthesis capability). You can imagine how useful would such a functionality be to a malicious app. Existing detection models can reliably predict when certain combinations of permissions requested by an app may pose problems. But because the Defensor apps mainly relied on obtaining Accessibility Service permissions from the user, along with some other minimalistic ones, no red flags were raised anywhere. The permissions requested by the app include the following, of which the critical ones are highlighted: android.permission.INTERNET android.permission.SYSTEM_ALERT_WINDOW android.permission.BIND_ACCESSIBILITY_SERVICE com.secure.protect.world.permission.C2D_MESSAGE android.permission.ACCESS_NETWORK_STATE android.permission.FOREGROUND_SERVICE android.permission.REQUEST_DELETE_PACKAGES android.permission.SYSTEM_OVERLAY_WINDOW android.permission.WAKE_LOCK android.permission.WRITE_SETTINGS com.google.android.c2dm.permission.RECEIVE In practice, this means the app can capture credentials entered by the user on mobile banking apps, read or generate SMS messages, read emails, read Two-Factor Authentication (2FA) codes generated by authenticator apps — thereby bypassing 2FA, steal cryptocurrency private keys, and so on, and upload all of this vital information to an attacker-controlled server! The app also requests the WAKE_LOCK permission, letting it override the default screen timeout setting, and keeping the device turned on persistently. This would give malware an extended opportunity to launch other apps and to continuously capturing sensitive information. The screenshots provided by ESET demonstrate this behaviour: Indicators of Compromise (IOCs) To make things easy for the security community, malware researchers at ESET have thankfully provided two useful IOCs identifying the malicious apps that have now been yanked from the Google Play store. Package Name SHA-1 Hash SHA-256 Hash ESET detection name com.secure.protect.world F17AEBC741957AA21CFE7C7D7BAEC0900E863F61 BBFB6DEDC01492CA3AC0C4F77343A22162518B306660E9CE958F2A6369FFAF13 Android/Spy.BanBra.A com.brazil.android.free EA069A5C96DC1DB0715923EB68192FD325F3D3CE B5A64791728AA641838D2A478375F5D46F91C91B8DF0CDE34B21DDA2D4D7D8A1 Android/Spy.BanBra.A New information and my analysis ESET researchers have done a brilliant job of presenting their comprehensive analysis of these apps and their documented behaviour. Further to their report however, I'd like to add a bit of my own findings. Command & Control (C&C) domains The attacker controlled C&C domains are still up — well at least one of them, and that's problematic. Domain IP address Task empresasenegocios.online 132.148.42.16 Command & Control (C&C) atendimentoempresarial.digital 184.168.221.46 Command & Control (C&C) The URLs specifically used by the app to establish communication between the attacker-controlled server include: https://empresasenegocios.online/remoteControl/ https://empresasenegocios.online/remoteControl/api/main/index/ http://atendimentoempresarial.digital/remoteControl/api/main/index http://atendimentoempresarial.digital/remoteControl/ Interestingly, VirusTotal reports most antivirus engines are still not flagging these URLs, except for FortiNet which flags just one of the empresasenegocios.online URLs as phishing: Nevermind the fact, the empresasenegocios.online domain still has a fancy admin panel for the attackers to log into and glance over the juicy details of their victims 🍿: Here's also a preview of the API: And the domain continues to be hosted on GoDaddy's shared hosting, with its beautiful cPanel and WebMail interfaces accessible: empresasenegocios.online/cpanel: empresasenegocios.online/webmail: At least, atendimentoempresarial.digital domain has its GoDaddy parking page showing up for now. While that's no guarantee that the domain's malicious ownership or activities have ceased, so far there are no strong signs indicating ongoing activity either. The WHOIS records of these domains didn't reveal anything particularly interesting other than Sãu Paulo, Brazil addresses and phone numbers, which could very likely be fakes, along with two email addresses belonging to the anonymous ProtonMail service: appdados@protonmail.com and notificador@protonmail.com. The Takeaways Enforcing BYOD policies Because prominent antivirus engines are not detecting apps like these — even now, advice to "scan your mobile device" is futile. SOC analysts and Security Ops professionals are strongly advised to enforce a corporate mobile device policy which restricts employee access to Google Play app store on their work devices. Apps like these pose significant threats to an organization's secrets especially when an organization has a relaxed Bring Your Own Device (BYOD) policy, allowing for corporate email accounts to be accessible on an employee's personal mobile device (e.g. Gmail's Android app managing both personal and work accounts of a user would not be immune to attacks like these, and could easily infiltrate corporate trade secrets to malicious actors). Network monitoring and blocks Additionally, extensive network monitoring in your SIEM/EDR products should be setup for these servers, with network blocks implemented, given at least one of these domains is still active. That way, any device on your corporate network would be prevented from inadvertently making calls to these domains. Note: The IP addresses appear to belong to GoDaddy's shared hosting, therefore blocking these could potentially block legitimate websites. It is best to block the malicious domains for the time being. DEFENSOR ID and Defensor Digital were just two of the apps which have been identified and removed from the Play store, but given their stealthy behaviour, we do not know as of yet how many other apps might be using these servers or leveraging the Accessibility Service weakness.$299.00
-
2 points
Time Left: 8 years and 1 month
- FOR SALE
- NEW
HOW IT WORKS ‼️ Everyone asks me in PM how the software works, what it finds, etc. In this post, I will try to explain how it all works for you guys. 1️⃣ Each cryptocurrency wallet has a mnemonic phrase that consists of 12 words, which gives access to your wallet on any device and from any crypto wallet app, such as Trust Wallet, Exodus, etc. 2️⃣ Behind those 12 words is a code that forms your Private Key which like the 12 words gives you access to your wallet. So, you're getting these 12 words when you create a wallet in any crypto wallet app and it's created automatically by a special algorithm. 3️⃣ In fact, we generate these 12 words according to a specific algorithm and check the presence of сoins on the wallets we find. 4️⃣ Then we check the balance of the wallets and give the result, which could be dozens of bitcoins that someone forgot on the wallets. In the end, after the software found the wallets with a balance, we enter the Private Key to the wallet with any application, Trust Wallet or Exodus for example, and just withdraw all coins found by the software to your wallet. Then CASH IT OUT! 💵 Any questions https://t.me/stealerbitcoin$400.00
-
2 points
Time Left: 5 years and 3 months
- FOR SALE
- NEW
The business has been operating for more than 8 years and brings regular profits. Business is 100% online. You can work from anywhere where there is Internet. Employment 2-3 hours a day. There are many options for customer traffic, everyone will find their own, not to the detriment of my business. At the moment, several dozen franchises have been launched, working regularly for profit. The payback period of the business is 1 month. The first client will arrive 7-10 days after the launch. The average check is $800 Max check 12000$ Business is the management of a trading platform - an exchange, and the sale of goods and services on it, the subject of business is specific, I will not specify what kind of goods, otherwise the topic will become public. And now about the most interesting thing, We have learned how to competently pull money out of the client's accounts, while he does not even understand how this happened and it is not possible to convict the organizers of anything. I give you a fishing rod, bring you to a fishing place and teach you how to fish. But you have to catch it, according to my methodology, letting everything take its course means losing. I won't say more about the specifics of the business. Many people have a question about the police? When they hear about illegal business. The police are not interested in this topic at all. Your clients won't even think of going there. Franchise price: The global version has 6 billion customers worldwide. Unlimited traffic flow. with 3 months of work, the profit is $ 10000+ Price 2500$ Next, you can scale (create copies) of your business yourself without asking me anything. Who do I want to see among the franchise buyers: Adequate people with substantive questions. He is polite and friendly with such people. People asking for alms are immediately blacklisted. Required Skills: - Confident use of the computer and the Internet. - The experience of communicating with people (all communication takes place online) And once again for everyone! You are buying a path to a stable online income, not the income itself. You should follow the instructions clearly, and not think that everything will come by itself. I will teach you how to run this business properly, with maximum income. It takes 2-3 days to deploy the project and transfer it to your hands. Then you study my instructions, ask questions and start working. I am always in touch, I will help with advice and business. There is also an option of joint cooperation of our businesses in the future, but only after the purchase.$2,500.00
-
2 points
Time Left: 7 years and 11 months
- FOR SALE
- NEW
All our documents are produced on high definition printers. They offer durability, exceptional print quality and an overall impression of quality and authenticity in our real identity pack (birth certificate,identity cards,drivers license passport,sim card ) . We offer a range of features such as barcodes, magnetic stripes, smart chips and holographic overlays. We also offer holographic over laminates, which adds authenticity to the cards. WE ALSO PRODUCE GENUINE DATABASE IDENTIFICATION PACKS FOR OTHER COUNTRIES TOO SO FEEL FREE TO CONTACT US WITH YOUR INQUIRY Refund Policy Refund/Reship policy 100 % refund or Reship Customers who have been loyal will get the best treatment.$3,500.00
-
2 points
Time Left: 5 years and 2 months
- FOR SALE
- NEW
GSM based skimmer, new technology, Power Supply from GAS pump. GSM and Power Supply from GAS pump means, you never need come back to GAS pump. Put it once inside GAS pump and just receive data, everywhere you want. All data is timestamped by time, seconds, day, month and year. Reads both bidirectional swipes (this means skimmer will read cards when they go in and also when they are pulled out. The button to power on and off skimmer is at the backside. Contains a red LED to show when it reads and gives errors on the skimmer. Comes with full manual included in the package. This product is guaranteed to be free from defects in materials and workmanship for 1 year since the date of purchase. We will, without charge, repair or replace at our option, any device returned for warranty work and found to be defective by us.$1,400.00
-
2 points
THIS ADVERT HAS EXPIRED!
- FOR SALE
- NEW
DeusEx ATM Jackpot How does it work? The DeusEx works on the Diebold Nixdorf and NCR ATMs world wide with big wall ATMs and the small ones. You will need to access the ATMs usb ports but they are easy to access, inserts a knife into the faceplate at the top of the ATM, it will flicks out, and exposes the ATMs USB port or drill a hole. There will be manuals included, instructions how it works in detail . Insert the USB stick and press CTRL+ENTER (more in manuals) and a normal Windows Explorer will popup from there browse to the USB stick and open the DeusEx or open cmd and enter the command (E):DeusExATM.exe You will need the following: – Knife or flat screwdriver for small ATMs – Drill with a hole saw/cutter for wall ATMs/(small ATMs) – USB hub (4x ports recommended) – Flashlight – Keyboard with inbuild touchpad or with a separate mouse (wired recommended) – USB Stick with LED (4GB recommended) – The DeusEx malware .exe (SDK just in case) DeusEx ATM Malware [latest] + Full source code – Manuals/Instructions included What is in the manuals? The tools you need, Extra Instructions, Tricks and AV bypass (just in case) How long does the ATM attack take? Depending on small or wall ATM but usually around a Minimum of 3 minutes max 10. Does it work world-wide with all ATM manufacturers? It works world-wide but it does only work with the Wincor Nixdorf and NCR ATMs. Does it bypass the AV? Yes it does, most of the ATMs doesn’t have AVs but there will be a manual include to bypass just in case.$1,000.00
-
1 point
Time Left: 8 years and 1 month
- FOR SALE
- NEW
To infect the device, it is enough for the user to click on the link or open the image. Up to $ 1000 per year with 1 connected device. The number of connected devices depends on you, there may be 10 or even 10,000. Antivirus programs do not react to infection in any way. Additional questions in telegram (https://t.me/misterpnh) or PM$999.00
-
1 point
-
1 point
-
1 point
Time Left: 5 years and 2 months
- FOR SALE
- NEW
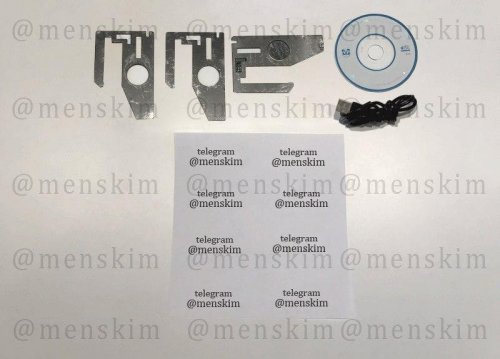
Ncr, Wincor Nixdor, Diebold Insert Skimmer.Full Kit ready for work.Battery can last up to 48 hours,outside temperature doesn’t affect to skimmer working time, because skimmer is located inside ATM.Store up to 15000 credit card tracks. Full Kit Include Insert and remove tools, data cable,software CD, this is plug and play product that is ready for work. Available to order PIN pad as extra option.$1,000.00
-
1 point
Time Left: 5 years and 2 months
- FOR SALE
- NEW
BARCLAYS SCAMPAGE .ZIP FILES UPLOAD AND UNZIP EDIT NECESSARY FILES WITH SOFTWARE OR ON SERVER UNDETECTABLE TO MANY SERVER INSTAT DELIVERY PLEASE CONTACT ME IF MORE HELP IS REQUIRED FOR ANY PRODUCT. DO NOT DISPUTE AN ORDER THE ADMIN IS VERY BUSY AND THEY WILL TAKE FOREVER TO SOLVE YOUR EMOTION ISSUES$200.00
-
1 point
Time Left: 5 years and 2 months
- FOR SALE
- NEW
PAYPAL SCAMPAGE .ZIP FILES UPLOAD AND UNZIP EDIT NECESSARY FILES WITH SOFTWARE OR ON SERVER UNDETECTABLE TO MANY SERVER INSTAT DELIVERY PLEASE CONTACT ME IF MORE HELP IS REQUIRED FOR ANY PRODUCT. DO NOT DISPUTE AN ORDER THE ADMIN IS VERY BUSY AND THEY WILL TAKE FOREVER TO SOLVE YOUR EMOTION ISSUES$200.00
-
1 point
Time Left: 5 years and 2 months
- FOR SALE
- NEW
WELLS FARGO SCAMPAGE .ZIP FILES UPLOAD AND UNZIP EDIT NECESSARY FILES WITH SOFTWARE OR ON SERVER UNDETECTABLE TO MANY SERVER INSTAT DELIVERY PLEASE CONTACT ME IF MORE HELP IS REQUIRED FOR ANY PRODUCT. DO NOT DISPUTE AN ORDER THE ADMIN IS VERY BUSY AND THEY WILL TAKE FOREVER TO SOLVE YOUR EMOTION ISSUES$200.00
-
1 point
THIS ADVERT HAS EXPIRED!
- FOR SALE
- NEW
⚠️ WARNING! ALL ITEMS ARE STRICTLY FOR EDUCATIONAL PURPOSES ONLY ;) AT YOUR OWN RISK! INSTANT DELIVERY! ⚠️ 💎 CARDINGS 💎 FRAUDS 💎 EXPLOITS 💎 LEAKS 💎 MALWARES 💎 MEGA AND GIGA PACKS 💎 AND OTHER GOODS! 💎 CHECK MY OTHER LISTINGS! GIVE POSITIVE FEEDBACK TO GET YOUR GIFT! WRITE DM IF FIND ANY ISSUE! Can mine all the following algorithms and thus all the cryptocurrencies that use them, so not only for XMR: cn/upx2, argon2/chukwav2, cn/ccx, kawpow, rx/keva, astrobwt, cn-pico/tlo, rx/sfx, rx/arq, rx/0, argon2/chukwa, argon2/wrkz, rx/wow, cn/fast, cn/rwz, cn/zls, cn/double, cn/r, cn-pico, cn/half, cn/2, cn/xao, cn/rto, cn-heavy/tube, cn-heavy/xhv, cn-heavy/0, cn/1, cn-lite/1, cn-lite/0 and cn/0. 2021 Software! Fast, secure, amazing! Make your own mining network and earn insane money, what you thought impossible! Main Features: - .NET - Coded in Visual Basic .NET, requires .NET Framework 4.5. - Codedom - No need for external libraries to compile - Injection (Silent) - Hide payload behind another process - CPU & GPU Mining - Can mine on Both CPU and GPU (Nvidia & AMD) - Idle Mining - Can be configured to mine with a different Max CPU when computer is idle - Stealth - Pauses the miner while Task Manager, Process Hacker or Process Explorer is open - Watchdog - Replaces the miner if removed and starts it if closed down - Remote Configuration - Can get the connection settings remotely from a URL at each startup - Bypass Windows Defender - Adds exclusions into Windows Defender for the general folders the miner uses - Online Downloader$599.00
-
1 point
THIS ADVERT HAS EXPIRED!
- FOR SALE
- NEW
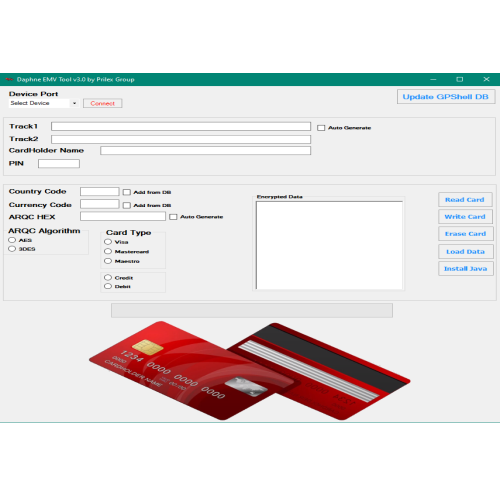
DAPHNE Latest software Because the latest Daphne version 2.0 is rarely supported due to the recent updates in the Security Industry, we come up with a new version of the most known and sophisticated EMV Chip Writer. This time, we gonna be selective with the persons we gonna sell the world’s most up-to-date EMV Chip Software. Anonymity is key here, there must be no leaks to the authorities so only the gentlemen that have the experience needed to operate such powerful software in a quiet manner and that can keep the discretion on theirs and our business will be able to receive Daphne What’s NEW with Daphne EMV Software ? • New improvements to the reclassify ARQC Algorithm. • New improvements to the Java Install on Smart Cards. • New writing methods for SDA & DDA and CDA Chips. • Added new compatibility of EMV Readers / Writers. • Optimized connection with GPShell DB. • The software is faster than ever and can handle multiple tasks. • New bypasser improvements for security level of ATMs & POS Terminals. • Added UpdateSys, that means the software receive automatically updates by our servers, a new version will be no longer neccesary in the future. • We also release new user’s manual with explicit content how to proper use Daphne EMV Software$199.00
-
1 point
THIS ADVERT HAS EXPIRED!
- FOR SALE
- NEW
This contains 13 really great methods to make a great living with carding. Besides different websites and techniques this are the highlights in the guides: - Top notch carding video's and pdfs - Anonimity, changing socks5 and top socks5 providers - The best way to connect RDP - Cashing out CC in front of YOU, making $250 in 15 minutes - CARDING SAMSUNG phones - Cashing out PAYPAL accounts$499.00
-
1 point
-
1 point
-
1 pointSize: 60Mb Lines: 1,2M [hide]https://anonfile.com/Q4qaBehdb9/nulled.to_private_txt[/hide]
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 pointRequires Proxies Yes Recommended No. of Bots - Default Combo Type Username/Email Password - Both Last Checked (9/24/2018) [hide] https://anonfile.com/U01bY3h5be/Origin_ini[/hide]
-
1 pointThanks man I been looking for good combo tools hope this is what i need and works well
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 pointnever tested thanks bro for the release
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 pointLooking goood with them releases keep it up boi
-
1 point
-
1 point
-
1 point
-
1 point












.thumb.png.833d8042a48b4bd59e7ed409fba6cd75.png)