Leaderboard
Popular Content
Showing content with the highest reputation on 12/16/2023 in all areas
-
3 points
Time Left: 6 years and 20 days
- FOR SALE
- NEW
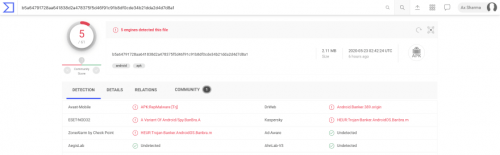
☢️ Dissecting DEFENSOR: a stealthy Android banking malware #android#apps#malware#mobile Android malware apps are nothing new, but this one is of particular interest in how it implements no such functionality that can be readily detected by security products. The apps named DEFENSOR ID and Defensor Digital rely mainly on Android's Accessibility Service to conduct malicious activities, and go undetected. In fact, a blog post released May 22nd 2020 by malware researcher Lukas Stefanko of ESET states, "the banking trojan was available on Google Play at the time of the analysis. The app is fitted with standard information-stealing capabilities; however, this banker is exceptionally insidious in that after installation it requires a single action from the victim – enable Android’s Accessibility Service – to fully unleash the app’s malicious functionality." The blog post also demonstrates at the time of its inception, no antivirus engine detected this malware sample. Even today, only 5-6 detection engines are flagging these two apps, according to VirusTotal. This raises concern for the next iteration of malware that may be nothing but a slight modification of these apps. Android Accessibility Service To make smartphones more accessible to users with special needs, the Accessibility Service allows for the device to extend permissions to an app to read screen content (e.g. for providing text to speech synthesis capability). You can imagine how useful would such a functionality be to a malicious app. Existing detection models can reliably predict when certain combinations of permissions requested by an app may pose problems. But because the Defensor apps mainly relied on obtaining Accessibility Service permissions from the user, along with some other minimalistic ones, no red flags were raised anywhere. The permissions requested by the app include the following, of which the critical ones are highlighted: android.permission.INTERNET android.permission.SYSTEM_ALERT_WINDOW android.permission.BIND_ACCESSIBILITY_SERVICE com.secure.protect.world.permission.C2D_MESSAGE android.permission.ACCESS_NETWORK_STATE android.permission.FOREGROUND_SERVICE android.permission.REQUEST_DELETE_PACKAGES android.permission.SYSTEM_OVERLAY_WINDOW android.permission.WAKE_LOCK android.permission.WRITE_SETTINGS com.google.android.c2dm.permission.RECEIVE In practice, this means the app can capture credentials entered by the user on mobile banking apps, read or generate SMS messages, read emails, read Two-Factor Authentication (2FA) codes generated by authenticator apps — thereby bypassing 2FA, steal cryptocurrency private keys, and so on, and upload all of this vital information to an attacker-controlled server! The app also requests the WAKE_LOCK permission, letting it override the default screen timeout setting, and keeping the device turned on persistently. This would give malware an extended opportunity to launch other apps and to continuously capturing sensitive information. The screenshots provided by ESET demonstrate this behaviour: Indicators of Compromise (IOCs) To make things easy for the security community, malware researchers at ESET have thankfully provided two useful IOCs identifying the malicious apps that have now been yanked from the Google Play store. Package Name SHA-1 Hash SHA-256 Hash ESET detection name com.secure.protect.world F17AEBC741957AA21CFE7C7D7BAEC0900E863F61 BBFB6DEDC01492CA3AC0C4F77343A22162518B306660E9CE958F2A6369FFAF13 Android/Spy.BanBra.A com.brazil.android.free EA069A5C96DC1DB0715923EB68192FD325F3D3CE B5A64791728AA641838D2A478375F5D46F91C91B8DF0CDE34B21DDA2D4D7D8A1 Android/Spy.BanBra.A New information and my analysis ESET researchers have done a brilliant job of presenting their comprehensive analysis of these apps and their documented behaviour. Further to their report however, I'd like to add a bit of my own findings. Command & Control (C&C) domains The attacker controlled C&C domains are still up — well at least one of them, and that's problematic. Domain IP address Task empresasenegocios.online 132.148.42.16 Command & Control (C&C) atendimentoempresarial.digital 184.168.221.46 Command & Control (C&C) The URLs specifically used by the app to establish communication between the attacker-controlled server include: https://empresasenegocios.online/remoteControl/ https://empresasenegocios.online/remoteControl/api/main/index/ http://atendimentoempresarial.digital/remoteControl/api/main/index http://atendimentoempresarial.digital/remoteControl/ Interestingly, VirusTotal reports most antivirus engines are still not flagging these URLs, except for FortiNet which flags just one of the empresasenegocios.online URLs as phishing: Nevermind the fact, the empresasenegocios.online domain still has a fancy admin panel for the attackers to log into and glance over the juicy details of their victims 🍿: Here's also a preview of the API: And the domain continues to be hosted on GoDaddy's shared hosting, with its beautiful cPanel and WebMail interfaces accessible: empresasenegocios.online/cpanel: empresasenegocios.online/webmail: At least, atendimentoempresarial.digital domain has its GoDaddy parking page showing up for now. While that's no guarantee that the domain's malicious ownership or activities have ceased, so far there are no strong signs indicating ongoing activity either. The WHOIS records of these domains didn't reveal anything particularly interesting other than Sãu Paulo, Brazil addresses and phone numbers, which could very likely be fakes, along with two email addresses belonging to the anonymous ProtonMail service: appdados@protonmail.com and notificador@protonmail.com. The Takeaways Enforcing BYOD policies Because prominent antivirus engines are not detecting apps like these — even now, advice to "scan your mobile device" is futile. SOC analysts and Security Ops professionals are strongly advised to enforce a corporate mobile device policy which restricts employee access to Google Play app store on their work devices. Apps like these pose significant threats to an organization's secrets especially when an organization has a relaxed Bring Your Own Device (BYOD) policy, allowing for corporate email accounts to be accessible on an employee's personal mobile device (e.g. Gmail's Android app managing both personal and work accounts of a user would not be immune to attacks like these, and could easily infiltrate corporate trade secrets to malicious actors). Network monitoring and blocks Additionally, extensive network monitoring in your SIEM/EDR products should be setup for these servers, with network blocks implemented, given at least one of these domains is still active. That way, any device on your corporate network would be prevented from inadvertently making calls to these domains. Note: The IP addresses appear to belong to GoDaddy's shared hosting, therefore blocking these could potentially block legitimate websites. It is best to block the malicious domains for the time being. DEFENSOR ID and Defensor Digital were just two of the apps which have been identified and removed from the Play store, but given their stealthy behaviour, we do not know as of yet how many other apps might be using these servers or leveraging the Accessibility Service weakness.$299.00
-
2 points
Time Left: 5 years and 2 months
- FOR SALE
- NEW
TD BANK SCAMPAGE .ZIP FILES UPLOAD AND UNZIP EDIT NECESSARY FILES WITH SOFTWARE OR ON SERVER UNDETECTABLE TO MANY SERVER INSTAT DELIVERY PLEASE CONTACT ME IF MORE HELP IS REQUIRED FOR ANY PRODUCT. DO NOT DISPUTE AN ORDER THE ADMIN IS VERY BUSY AND THEY WILL TAKE FOREVER TO SOLVE YOUR EMOTION ISSUES$200.00
-
2 points
THIS ADVERT HAS EXPIRED!
- FOR SALE
- NEW
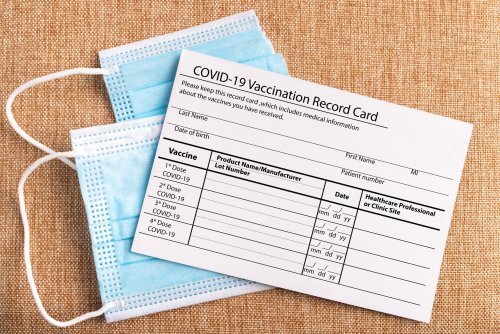
If you need Information on how to obtain Covid-19 Vaccine Cards or information on how to Get a certificate indicating that you’ve been vaccinated, known as the Pass Sanitaire (Covid 19 Sanitary pass) or Pass Vaccinal in France Get a French/European “covid health pass” , EU or France Certificate, French Vaccine Pass, EU Covid-19 “passport“, covid pass french without the Covid-19 Vaccin with us via our email. We also produce False certificate vaccine of covid or falsified a health pass with QR codes.$300.00
-
2 points
THIS ADVERT HAS EXPIRED!
- FOR SALE
- NEW
Description IMPORTANT! -100% Guarantee! IMPORTANT! -Instant Delivery! IMPORTANT! -Request your bonus after positive feedback! Item description: About me: I am a carder myself with more than 10 years of experience! With the Cashout Methods I am using myself and now offering to you guys you can easily make up to 4000 - 6000 $/£ per DAY Easily! All methods are based on my own experiences. Again: I am using all methods by myself and they work 100 You can make thousands of dollars/Pounds every single day when mastering these methods Some methods are so simple you can't do anything wrong!!! I promise! You will get: - 5 proven step-by-step CASHOUT METHODS that are working 100% (All up to date - 2021! n easy to follow even for BEGINNER) - list of legit darkweb CVV VENDORS I am using myself (Never get scammed again!) - list of CARDABLE SITES (Never kill card due to high security level of website!) Once ordered you will get a download link with PDF Guide which contains all information mentioned above Refund policy Please Give Me Enough Time To Reply To You Before You Leave A Review (If You Have A Problem) Kind Regards$229.00
-
2 points
THIS ADVERT HAS EXPIRED!
- FOR SALE
- NEW
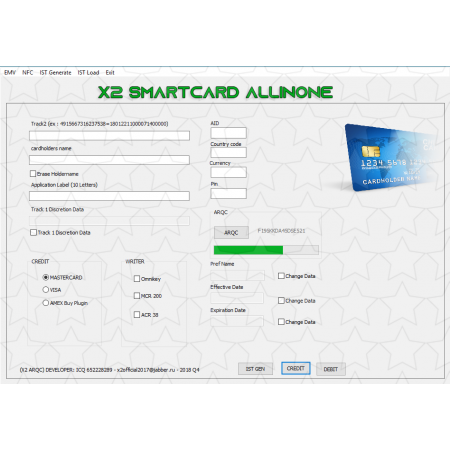
Development Notes: Functioning with over 20 Different EMV Writers Used with 1 Encryption code for functionality. Updated frequently to combat Patches from Banks. When banks and other financial institutions introduced chip-based cards, or to be more specific EMV cards, they claimed they were safer. These cards encoded payment information on a microchip. The generation of a one-time use cryptogram further enhanced security of these cards. EMVs were regarded as an upgrade from magstripe cards. And while the world breathed a sigh of relief, believing that their financial transactions were secure, DeepTeam have been busy devising methods to break the barriers of EMV cards. Modern EMV card reader software developed by DeepTeam not only skim data from POS and ATM machines, software can also clone cards. These fake EMV cards are further used to complete cash withdrawals and buy products off the market. The EMV software is one of such EMV reader writer software solutions available on the market. Here’s more on the features of EMV reader-writer software’s and how they work. POS (Point of Sale Machines Compromised) EMV cloning software is designed to read, write, erase, encode and duplicate EMV. In order to complete any of these processes, it requires credit and debit card information that it can copy onto these cards. Thus, the first step is to collect payment card data, often done through using shady means. Scammers compromise point-of-sale systems or ATMs using shimmers. These are unlike the card slot or keypad look-alike fixtures fitted to a sales terminal or ATM. The ‘shimmers’ are paper-thin inserts that fit into the card slot on a point-of-sale terminal. They have an embedded microchip of their own, that steals and stores credit and debit card data every time a person uses their card to make a payment or withdraw cash. The purloined chip data is stored in the device. Again, the skimmers have been updated. While earlier the data skimmer would have to be physically retrieved, modern day skimmer dispenses with it. They are designed to be remotely controlled and transmit data directly via SMS. Dumps The data thus stolen is either used to clone cards or further packaged and sold as dumps to customers. These dumps are used to burn and write cloned cards. Data is stored in the form of tracks on a payment card. The patch helps gather crucial track data needed to complete a transaction such as cardholder name, account number and expiration date. Cloning Cards An EMV reader writer software allows one to clone and create their own cards that work at almost all point of sale systems. Once connected to the hardware, the EMV card reader software enables multiple functionalities. There are templates for different credit card structures. You can choose from a range of card formats – Visa, MasterCard, Maestro, American Express, Discover and Diners Club. One can also choose between a credit and debit card. The software runs the necessary tests after which the information is transferred to the new card by means of an EMV writer software. The transfer takes place via GPShell script. The new card created is as good as the original. A well-designed user interface makes credit card cloning a breeze. EMV reader writer software is a complete malware suite and makes cloning a hassle free task.$199.00
-
2 points
THIS ADVERT HAS EXPIRED!
- FOR SALE
- NEW
NFC ATM Jackpotting Malware. Works only at NCR SelfServ NCR ProCash modes (WORLDWIDE). Withdraws all cassettes one-by-one. DOESN'T REQUIRE USB ACCESS OR ANY PHYSICAL INSIDE ACCESS. Injects through NFC card. You will need a very specific software to use it. I'll help with links where you can buy it. Overall spendings will be around 50-100 USD. I will stop selling at any time. As soon as I realize that too many people use it.. Manual and safety guide will be included with software. Any technical details won't be shared until funds are in escrow.$2,200.00
-
1 point
-
1 point[hide]https://drive.google.com/drive/folders/0BwyWDQ59jRVGMFp3UnBfeUEzanM[/hide] Like the post and share
-
1 point
Time Left: 5 years and 3 months
- FOR SALE
- NEW
My team and I will deliver any product from Amazon or Ebay for 40%. The service of receiving parcels by drop is free of charge. You receive the package from us, not from the store. Only you know about the origin of this product, so it is safe. Min. order 250$ ( My share)$250.00
-
1 point
-
1 point
-
1 point
Time Left: 5 years and 2 months
- FOR SALE
- NEW
PAYPAL SCAMPAGE .ZIP FILES UPLOAD AND UNZIP EDIT NECESSARY FILES WITH SOFTWARE OR ON SERVER UNDETECTABLE TO MANY SERVER INSTAT DELIVERY PLEASE CONTACT ME IF MORE HELP IS REQUIRED FOR ANY PRODUCT. DO NOT DISPUTE AN ORDER THE ADMIN IS VERY BUSY AND THEY WILL TAKE FOREVER TO SOLVE YOUR EMOTION ISSUES$200.00
-
1 pointView Advert SCAMPAGE NATWEST NATWEST SCAMPAGE .ZIP FILES UPLOAD AND UNZIP EDIT NECESSARY FILES WITH SOFTWARE OR ON SERVER UNDETECTABLE TO MANY SERVER INSTAT DELIVERY PLEASE CONTACT ME IF MORE HELP IS REQUIRED FOR ANY PRODUCT. DO NOT DISPUTE AN ORDER THE ADMIN IS VERY BUSY AND THEY WILL TAKE FOREVER TO SOLVE YOUR EMOTION ISSUES Advertiser F*ck FBI Date 11/17/2021 Price $200.00 Category Sites
-
1 pointView Advert SCAMPAGE DESJARDINS DESJARDINS SCAMPAGE .ZIP FILES UPLOAD AND UNZIP EDIT NECESSARY FILES WITH SOFTWARE OR ON SERVER UNDETECTABLE TO MANY SERVER INSTAT DELIVERY PLEASE CONTACT ME IF MORE HELP IS REQUIRED FOR ANY PRODUCT. DO NOT DISPUTE AN ORDER THE ADMIN IS VERY BUSY AND THEY WILL TAKE FOREVER TO SOLVE YOUR EMOTION ISSUES Advertiser F*ck FBI Date 11/17/2021 Price $200.00 Category Sites
-
1 pointView Advert SCAMPAGE SCOTIABANK SCOTIABANK SCAMPAGE .ZIP FILES UPLOAD AND UNZIP EDIT NECESSARY FILES WITH SOFTWARE OR ON SERVER UNDETECTABLE TO MANY SERVER INSTAT DELIVERY PLEASE CONTACT ME IF MORE HELP IS REQUIRED FOR ANY PRODUCT. DO NOT DISPUTE AN ORDER THE ADMIN IS VERY BUSY AND THEY WILL TAKE FOREVER TO SOLVE YOUR EMOTION ISSUES Advertiser F*ck FBI Date 11/17/2021 Price $200.00 Category Sites
-
1 point
THIS ADVERT HAS EXPIRED!
- FOR SALE
- NEW
NFC ATM Jackpotting Malware. Works only at NCR SelfServ NCR ProCash modes (WORLDWIDE). Withdraws all cassettes one-by-one. DOESN'T REQUIRE USB ACCESS OR ANY PHYSICAL INSIDE ACCESS. Injects through NFC card. You will need a very specific software to use it. I'll help with links where you can buy it. Overall spendings will be around 50-100 USD. I will stop selling at any time. As soon as I realize that too many people use it.. Manual and safety guide will be included with software. Any technical details won't be shared until funds are in escrow.$2,500.00
-
1 pointDon't Forget Click Like For Me [hide] Imm06@comcast.net:Giroux28 | Count = 1 | Title#1 = complete-guitar-system-beginner-to-advanced | dhayman67@hotmail.com:romanroad67 | Count = 2 | Title#1 = draft/151248 | Title#2 = makeup-effortless-makeup-for-real-women | imax09@gmail.com:max923 | Count = 0 | Title#1 = | edible_sandwich@yahoo.com:qa12zx34 | Count = 0 | Title#1 = | domainlinks@auto-glass-houston.com:domainlinks | Count = 0 | Title#1 = | nganesan@buffalo.edu:Naveeng8 | Count = 1 | Title#1 = adobe-indesign-made-easy | saneea_abboud@hotmail.com:Gregory4 | Count = 1 | Title#1 = freedom-to-choose-something-different-by-pema-chodron-pt-1 | maryanndavenportst@gmail.com:z2684615z | Count = 0 | Title#1 = | alanbotox@gmail.com:oxi123 | Count = 0 | Title#1 = | mekson.dee@gmail.com:722074 | Count = 1 | Title#1 = learn-html5-programming-from-scratch | ronan@drivenhear.com:galaxy321 | Count = 1 | Title#1 = cold-emailing-for-business | ma_ty_ya@hotmail.com:dsaasd | Count = 1 | Title#1 = draft/117160 | smishdesigns@gmail.com:Shivangam88 | Count = 0 | Title#1 = | wan_well_harry@hotmail.com:049726636 | Count = 3 | Title#1 = design-and-develop-a-killer-website-with-html5-and-css3 | Title#2 = the-complete-javascript-course | Title#3 = beerbrewing | administrator@crobads.com:Qazwsx111$ | Count = 0 | Title#1 = | resondrums@gmail.com:resandapple | Count = 0 | Title#1 = | knorton-schock@ardentcause.com:3387848 | Count = 1 | Title#1 = draft/691912 | [/hide]
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point[hide] Combo: davidf76@cox.net:Sandiego1 Date: 6/29/2018 8:58:47 AM Total Charge: USD 15.00 Date: 6/27/2018 9:37:54 AM Total Charge: USD 10.00 Combo: gmcrocker@dcwisp.net:mel5rose Date: 1/5/2016 4:41:03 AM Total Charge: USD 0.01 [/hide]
-
1 pointFortnite - 1,000 V-Bucks [04.05.18] Fortnite - 2,500 (+300 Bonus) V-Bucks [23.02.18] Call of Duty®: WWII [02.02.18] Battlefield Bundle [22.01.18] theHunter: Call of the Wild [16.01.18] Overwatch League™ - 100 League Tokens [12.01.18] Gang Beasts [09.01.18] PS Plus: 12 Month Membership [25.12.17] Battlefield™ 1 Shortcut Kit: Scout Bundle [17.09.17] Battlefield™ 1 Revolution [30.08.17] Destiny - The Collection [12.02.17] ARK: Survivor's Pack [09.02.17] [hide] Credentials: nmgould99@gmail.com:Braykennel1 PsnID: bdog1069 Country: US Date of checking: 30.09.18 16:17:14 -------------------- Fortnite - 1,000 V-Bucks [04.05.18] Fortnite - 2,500 (+300 Bonus) V-Bucks [23.02.18] Call of Duty®: WWII [02.02.18] Battlefield Bundle [22.01.18] theHunter: Call of the Wild [16.01.18] Overwatch League™ - 100 League Tokens [12.01.18] Gang Beasts [09.01.18] PS Plus: 12 Month Membership [25.12.17] Battlefield™ 1 Shortcut Kit: Scout Bundle [17.09.17] Battlefield™ 1 Revolution [30.08.17] Destiny - The Collection [12.02.17] ARK: Survivor's Pack [09.02.17] -------------------- [/hide]
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 pointNIIIICE!! THank you!! Awesome upload.... Good job Brotha
-
1 pointlet me check this tools thank you
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point[align=center][hide] https://www69.zippyshare.com/v/N5APDsdj/file.html [/hide][/align] Leave a Like
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point









.thumb.jpg.54fe612db4266020538ed9f310d58398.jpg)




